The latest crippling ransomware to hit our digital world has been Wanna Cry, which raised its head around May 12. Ransomware is a kind of software used by bad actors (or simply put “bad guys”) to make data in computer systems unavailable, such as, by encrypting the data. The bad actors promise to make the data available again upon payment of ransom, typically in the form of digital currency that cannot be easily traced back. In this case, the Wanna Cry authors asked for ransom roughly equivalent to $300 in bitcoin.
One of the two main reasons Wanna Cry thankfully did not do as much damage as had been originally feared is that the hackers writing the ransomware had made an elementary mistake. Here is the reason, abstracting out the more technical details. (A wonderful technical description has been given by MalwareTech, the person who uncovered the defense in the first place.)
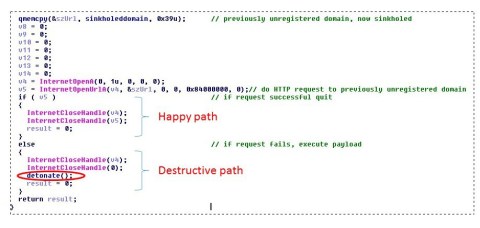
The ransomware queries for a garbled-looking URL and if it gets a successful response to the query, it suspects it is being run within a sandbox (a fake environment designed by security administrators/defenders to observe the malware in action). In that case the malware shuts down. In the enclosed code fragment, you can see where I have highlighted the happy path (where WannaCry shuts itself down) and the unhappy path (where WannaCry detonates and does its deed). The MalwareTech security researcher simply bought the unregistered garbled-looking domain for the princely sum of $10.69 causing WannaCry to take the happy path.
Now we can theorize why the WannaCry authors did this? It is fairly elementary to randomize URLs, rather than a hard-coded one. Domain generation algorithms (DGAs) are fairly commonly used and there are many tools publicly available for DGAs. Many prior malwares (Conficker, first detected in 2008 is a prime example) have used DGAs. So why did these guys not use DGA. First off, let us thank our lucky stars that they did not. With that off the chest, let us theorize.
First theory is that the WannaCry authors wanted to have a kill switch that they could use in case they wanted to rein in the spread of their creation. So in this version they did not anticipate that if they had the kill switch, the same switch could be used by the good guys as well. A classic case of dual use technology, but now slightly in reverse.
Second theory is that the WannaCry authors got lazy and copy-and-pasted this part of the code from prior malwares and did not copy-and-paste the earlier parts of the code which used the DGA. The earlier part may actually come quite a bit before (in spatial or lines of code terms) than the “checking if I am in a sandbox” part. So if you do not know to look that far above, you will miss the randomization code.
My personal opinion — remember I said opinion — is that the second of two theories is correct. So we have a case of lazy (or careless) but not downright stupid hackers here. Now of course, in the classic cat-and-mouse security landscape, variants of the ransomware are coming out where random URL generation is indeed being used. So this simple kill switch will not work. But like in the good guys’ work, it is better to get it right the first time. So with the first generation of the ransomware figured out, system owners took the defense of patching their system (old versions of Windows such as Windows XP), which removed the basic exploit that the ransomware was targeting
This case points out a fundamental dilemma of computer system owners and computer software vendors. Windows XP had reached its end of life way back in April 2014, and yet there are many many systems running Windows XP today. A major outbreak like WannaCry raises the public consciousness and vendors’ call to action, but all the other attacks which do not rise to this level, would likely have been infecting these outdated systems.
We are embracing the Internet of Things (IoT) brave new world. I bet some of you have refrigerators from 5+ years back and thermostats from that far back. If they were smart and relied on updates from vendors and vendors due to economic imperatives, quite independent of your or my needs, decided that these appliances had reached their end-of-life, what would we do? Well thank heavens Best Buy with the latest version of the smart appliance will be close at hand.